In today’s digital age, where concerns about privacy and security loom large, the term “IMEI number” often sparks curiosity and sometimes even paranoia. But fret not, dear reader! Let’s delve into the world of IMEI numbers to demystify their purpose, functionality, and implications.
What Is an IMEI Number on a Cell Phone?
So, what exactly is this IMEI number that everyone seems to talk about? Well, put simply, the IMEI number (International Mobile Station Equipment Identity Number) is a unique identifier assigned to mobile devices operating on terrestrial cellular networks. It serves as a digital fingerprint for your phone, distinguishing it from millions of others in the network.
Fun Fact: IMEI numbers are not exclusive to smartphones; other devices like laptops and tablets equipped with cellular capabilities also carry IMEI numbers.
How Does an IMEI Number Work?
Now that we know what an IMEI number is, let’s unravel its functionality. IMEI numbers play a crucial role in facilitating communication between your device and cellular networks. Additionally, they serve as a deterrent against theft. If your phone is stolen and you report it, the IMEI number can be used to block the device from accessing cellular networks, rendering it practically useless to the thief.
Government Tracking Using IMEI Numbers
You might wonder, does the government use IMEI numbers to spy on citizens? Well, the truth is less sinister than some may fear. While governments can track devices using IMEI numbers with proper legal authorization, they do not possess the capacity to identify individual users based solely on IMEI numbers. Rest assured, your privacy remains intact unless you engage in illicit activities that warrant government scrutiny.
Not All Devices Have IMEI Numbers
Surprisingly, not every phone boasts an IMEI number. Devices lacking this identifier are often counterfeit or subpar in quality, posing potential risks to users’ privacy and security. Moreover, some speculate that government agencies utilize phones without IMEI numbers to evade surveillance—a notion that underscores the importance of authenticating your device’s legitimacy.
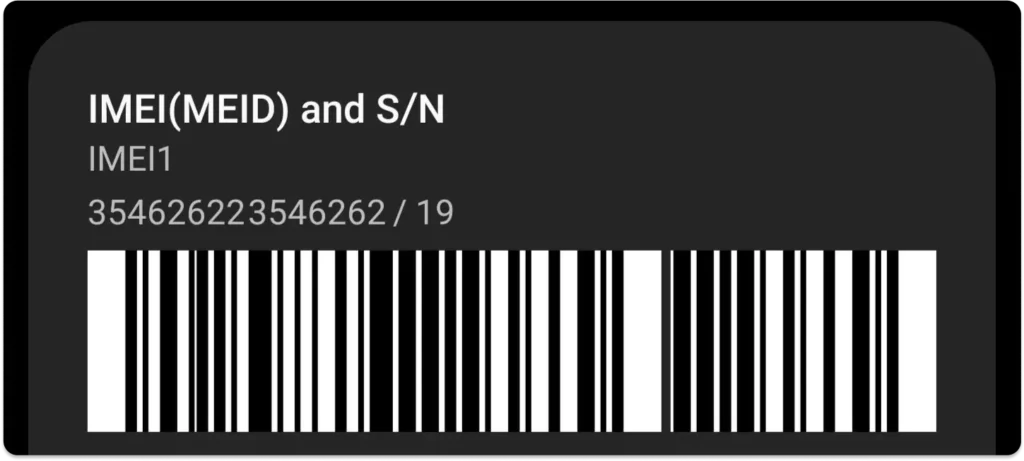
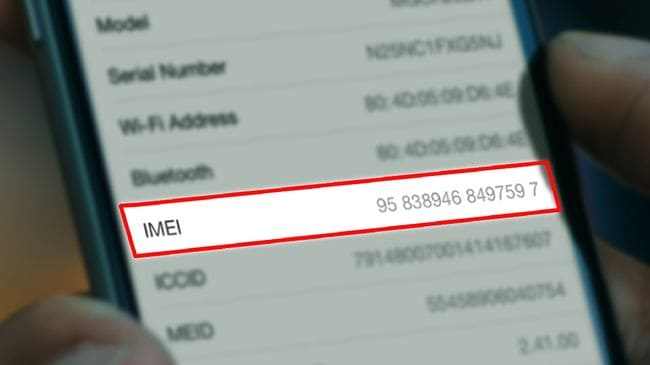
How to Check the IMEI Number
Curious about your device’s IMEI number? Fret not, as there are multiple methods to uncover this digital fingerprint:
| Method | Description |
|---|---|
| Dialing *#06# | Simply dial *#06# on your device’s keypad, and the IMEI number will be displayed on the screen. |
| Settings Menu | Navigate to your device’s settings menu, select “About Phone” or similar, and locate the IMEI information. |
| Original Packaging | The IMEI number is often printed on the original packaging of your device, making it easily accessible. |
Benefits of IMEI Numbers
Despite apprehensions surrounding IMEI numbers, they offer numerous benefits:
- Anti-Theft Measures: IMEI numbers serve as a powerful deterrent against phone theft, enabling swift blocking of stolen devices on cellular networks.
- Device Authentication: IMEI numbers validate the authenticity of devices, safeguarding users against counterfeit products.
- Secondhand Purchase Safety: Before buying a used phone, you can verify its legitimacy and check for blacklisting using IMEI numbers.
Can IMEI Be Used for Hacking?
Contrary to popular belief, hacking a device solely through its IMEI number is improbable. While rumors suggest otherwise, gaining access to sensitive information or compromising a device’s security via IMEI numbers is highly unlikely. It’s essential to exercise caution and adhere to cybersecurity best practices to mitigate potential risks.
Is Changing IMEI Illegal?
Yes, altering an IMEI number is illegal in many jurisdictions. This unique identifier, assigned by manufacturers, serves as a crucial tool for mobile networks to track and identify devices. Tampering with IMEI numbers can lead to legal consequences, including fines and imprisonment.
Difference Between an ESN and an IMEI
While both Electronic Serial Numbers (ESNs) and IMEI numbers fulfill similar roles as device identifiers, they differ in several aspects:
| Aspect | ESN | IMEI |
|---|---|---|
| Usage | Primarily used by CDMA networks | Utilized by all types of mobile networks (GSM, CDMA, etc.) |
| Allocation | Allocated by the carrier | Allocated by the device manufacturer |
| Network Compatibility | Exclusive to CDMA networks | Compatible with all types of mobile networks |
| Activation Eligibility Check | Determines eligibility for activation on CDMA networks | Identifies devices for tracking, blacklisting, and theft prevention across various networks |
Signs Your Phone Might Be Hacked
Concerned about potential phone hacking? Look out for these warning signs:
- Battery Drain: Sudden and excessive battery drain may indicate unauthorized background processes.
- Unusual Data Usage: An abrupt surge in data consumption could signal data exfiltration by hackers.
- Presence of Unfamiliar Apps: Unauthorized installation of unknown apps suggests malware infiltration.
- Strange Texts or Emails: Outgoing messages or emails you didn’t send may indicate compromised accounts.
- Slow Performance: Sluggish operation could signify unauthorized resource consumption by malicious software.
Why You Shouldn’t Share Your IMEI
Protecting your IMEI number is crucial to safeguarding your privacy and security. Avoid sharing your IMEI number to prevent potential misuse or exploitation by malicious actors. Remember, keeping your IMEI confidential is the first step towards preserving your digital well-being.
Conclusion
In essence, IMEI numbers serve as indispensable tools for device identification and theft prevention in the mobile landscape. While concerns about privacy and security abound, understanding the functionality and limitations of IMEI numbers alleviates unnecessary apprehensions. By adhering to best practices and exercising caution, users can harness the benefits of IMEI numbers while mitigating associated risks.
Now that we’ve explored the realm of IMEI numbers, let’s embrace technology’s wonders while staying vigilant against potential threats.
Frequently Asked Questions
- Can someone track my location using my IMEI number?
- No, IMEI numbers alone cannot track your location. They serve as device identifiers and do not provide location data.
- Is it safe to share my IMEI number with mobile carriers?
- Yes, sharing your IMEI number with authorized entities like mobile carriers is generally safe and necessary for device activation and support.
- Can I change my device’s IMEI number?
- No, changing IMEI numbers is illegal in many jurisdictions and can lead to severe penalties.
- How can I protect my device from hacking attempts?
- To safeguard your device, ensure it is regularly updated with the latest security patches, avoid suspicious links or downloads, and use reputable antivirus software.
- Are there any legitimate uses for accessing someone else’s IMEI number?
- Legitimate uses include verifying the authenticity of a secondhand device before purchase or reporting a stolen device to authorities.
- Does every mobile device have an IMEI number?
- While most legitimate mobile devices possess IMEI numbers, counterfeit or unauthorized devices may lack this identifier.
- Can IMEI numbers be traced back to individual users?
- No, IMEI numbers alone do not contain personal information and cannot be used to identify individual users without additional context or authorization.
- What should I do if I suspect my phone has been hacked?
- If you suspect your phone has been compromised, immediately disconnect it from the internet, change your passwords, and seek assistance from cybersecurity experts or device manufacturers.
- Can IMEI numbers be used to block stolen devices internationally?
- Yes, mobile networks can block stolen devices internationally using IMEI numbers, rendering them unusable on cellular networks worldwide.
- Are there any alternatives to IMEI numbers for identifying mobile devices?
- While IMEI numbers are widely used, other identifiers such as serial numbers and MAC addresses may also serve similar purposes in certain contexts.